Network security is a critical aspect of any organization’s cybersecurity strategy. With the increasing number of cyber threats and attacks, it is essential to implement controls and monitoring systems to protect sensitive data.
An audit of network security involves the systematic examination of an organization’s network infrastructure to identify and assess vulnerabilities. This audit includes penetration testing, which simulates real-world cyber attacks to evaluate the resilience of the network against intrusion.
Access controls play a crucial role in network security. Implementing robust authentication and authorization mechanisms ensures that only authorized personnel can access sensitive data and systems. Regular audits can identify weak access control measures and recommend improvements.
Incident response is another critical aspect of network security. Timely detection and response to security incidents can help mitigate potential risks and minimize the impact of a cyber attack. Logging and monitoring systems are essential for effective incident response, as they provide valuable evidence and insights into the nature of the incident.
Compliance with industry standards and regulations is also vital for network security. Regular audits can ensure that the organization is meeting the necessary compliance requirements and taking the necessary steps to protect sensitive data. Firewalls, intrusion detection systems, and vulnerability assessments are some of the measures that can help achieve compliance.
Contents
- 1 Auditing Network Security
- 2 Importance of Network Security Auditing
- 3 Best Practices for Network Security Auditing
- 4 Strategies for Ensuring Data Protection
- 5 FAQ about topic “Auditing Network Security: Best Practices and Strategies for Ensuring Data Protection”
- 6 What are the best practices for auditing network security?
- 7 How can I ensure data protection in my network?
- 8 What are the risks of not auditing network security?
- 9 How often should network security audits be performed?
- 10 What are the common challenges faced in auditing network security?
Auditing Network Security

Network security is a critical aspect of protecting an organization’s sensitive data and infrastructure. Auditing network security involves evaluating the current state of the network and identifying potential risks, as well as implementing measures to address these risks.
One of the key components of auditing network security is incident response. This involves monitoring the network for any suspicious activity and promptly responding to any potential intrusions. By detecting and responding to potential threats in a timely manner, organizations can mitigate the risk and minimize the impact of security incidents.
Access control is another important aspect of auditing network security. This involves implementing strong authorization and authentication measures to ensure that only authorized individuals can access the network and its resources. By properly controlling who has access, organizations can reduce the risk of unauthorized access or data breaches.
Regular vulnerability assessments and penetration testing are also essential for auditing network security. These assessments help identify any weaknesses or vulnerabilities in the network that could potentially be exploited by attackers. By uncovering and addressing these vulnerabilities, organizations can strengthen their security controls and reduce the risk of a successful intrusion.
Compliance is another crucial aspect of auditing network security. Organizations need to ensure that their network security measures align with relevant industry regulations and standards. This involves conducting regular compliance assessments to ensure that the organization is meeting all necessary requirements.
Logging and monitoring are important for auditing network security as well. By keeping detailed logs of network activity and monitoring these logs for any suspicious or anomalous behavior, organizations can quickly detect and respond to potential security incidents. Additionally, implementing robust security controls such as firewalls can help prevent unauthorized access and protect the network from potential threats.
In conclusion, auditing network security is a complex and ongoing process that involves assessing the network’s security controls, detecting vulnerabilities, and implementing measures to address these vulnerabilities. By regularly auditing network security, organizations can reduce the risk of security incidents, protect sensitive data, and ensure the overall integrity of the network.
Importance of Network Security Auditing
Network security auditing plays a crucial role in safeguarding sensitive data and protecting against potential security risks. Through a comprehensive analysis of network systems and infrastructure, organizations can identify vulnerabilities and weaknesses that may pose a threat to their network security.
Risk assessment is a fundamental element of network security auditing. By assessing potential risks and vulnerabilities, organizations can implement appropriate controls and measures to mitigate these risks effectively. This includes ensuring proper authorization and authentication processes, implementing firewalls and intrusion detection systems, and monitoring network activities for any suspicious incidents.
Regular audits enable organizations to assess the effectiveness of their security controls and identify any gaps or areas for improvement. It allows them to evaluate the compliance of their network security practices with relevant regulations, standards, and industry best practices. By conducting penetration testing and vulnerability assessments, organizations can proactively detect and address any potential weaknesses in their network infrastructure.
Incident response and logging are important components of network security auditing. By maintaining logs of network activities, organizations can track and investigate any potential security breaches or unauthorized access attempts. This can aid in identifying the source of the incident, assessing the impact, and implementing appropriate measures to mitigate further risks.
Network security auditing also ensures that proper monitoring and authentication mechanisms are in place. It helps organizations verify the effectiveness of their network security controls and identify any unauthorized access attempts or suspicious activities. By implementing strong authentication protocols, organizations can mitigate the risk of unauthorized access to their network systems.
In conclusion, network security auditing is essential for organizations to maintain a secure network environment and protect valuable data. By regularly assessing and auditing their network systems, organizations can identify and mitigate potential vulnerabilities, ensure compliance with relevant regulations, and enhance overall network security.
Identifying Vulnerabilities
Identifying vulnerabilities is a crucial aspect of auditing network security. It involves a comprehensive assessment of the network environment to identify potential weaknesses or flaws that could be exploited by malicious individuals. This process typically involves several techniques and tools, such as logging and monitoring systems, authorization controls, and firewalls.
Logging and monitoring play a significant role in identifying vulnerabilities. By analyzing logs and monitoring network activities, security professionals can detect any unusual or suspicious behavior that may indicate a potential vulnerability. Through this process, they can identify unauthorized access attempts, intrusion attempts, and other security incidents that could potentially compromise the network’s integrity.
Authorization controls, such as user authentication and access levels, are also crucial in identifying vulnerabilities. These controls help ensure that only authorized individuals have access to sensitive data or system resources. By implementing strong authentication mechanisms, such as multi-factor authentication, organizations can reduce the risk of unauthorized access and potential vulnerabilities.
Network firewalls are essential components of network security that help identify vulnerabilities. They act as a barrier between internal and external networks, monitoring and controlling network traffic. By analyzing incoming and outgoing traffic, firewalls can detect and block any malicious or suspicious activities that may indicate potential vulnerabilities.
Penetration testing and compliance assessments are also effective methods of identifying vulnerabilities. Penetration testing involves simulating real-world attacks to identify security weaknesses. Compliance assessments, on the other hand, ensure that the network adheres to relevant security standards and regulations. These assessments help organizations identify potential vulnerabilities and address them accordingly.
In conclusion, identifying vulnerabilities is a crucial step in auditing network security. Through the use of logging and monitoring systems, authorization controls, firewalls, penetration testing, compliance assessments, and other security measures, organizations can effectively assess the network environment and address any potential weaknesses. By proactively identifying and addressing vulnerabilities, organizations can enhance their overall security posture and protect their data from potential threats.
Preventing unauthorized access to a network is crucial for maintaining data security and protecting sensitive information. To achieve this, organizations must implement a range of strategies and best practices that focus on analysis, authentication, assessment, risk detection, and audit.
One key strategy for preventing unauthorized access is implementing strong authentication measures. This involves using multifactor authentication, such as a combination of passwords and biometric verification, to ensure that only authorized individuals can access the network. Regular assessments of authentication systems should also be conducted to identify any vulnerabilities or weaknesses and to implement appropriate controls.
Risk assessment is another essential practice for preventing unauthorized access. By analyzing and assessing potential risks, organizations can identify vulnerabilities in their network and develop appropriate strategies to mitigate them. This includes regularly conducting penetration testing, which simulates a real-world attack to identify any potential weaknesses in the network’s defenses.
Compliance with security standards is also vital for preventing unauthorized access. Organizations should maintain detailed logs and records of user activity, ensuring that all access and authorization events are logged. This can assist in detecting any unauthorized access attempts and provide valuable information for incident response processes.
Implementing robust network security measures, such as firewalls and intrusion detection systems, is essential for preventing unauthorized access. Firewalls help control incoming and outgoing network traffic, while intrusion detection systems monitor network activity for signs of unauthorized access or malicious activity.
Regular audits should be conducted to assess the effectiveness of security controls in preventing unauthorized access. These audits can identify any vulnerabilities or weaknesses and enable organizations to take appropriate measures to strengthen their network security. In the event of an incident or breach, a well-defined incident response plan should be in place to facilitate a swift and effective response to protect against unauthorized access and minimize the impact.
Overall, preventing unauthorized access requires a comprehensive approach that includes robust authentication measures, regular assessments of network vulnerabilities, compliance with security standards, and the implementation of strong security controls. By following these best practices, organizations can minimize the risk of unauthorized access and protect their sensitive data and information.
Best Practices for Network Security Auditing
Network security auditing is essential for ensuring the protection of data and mitigating risks. By implementing best practices, organizations can effectively analyze and monitor the security of their network infrastructure. Below are some key best practices for network security auditing:
- Access Controls: Implement strong access controls to restrict unauthorized access to sensitive information. This includes using strong passwords, multi-factor authentication, and regular access reviews.
- Firewall Configuration: Regularly review and update firewall configurations to ensure that only necessary network traffic is allowed and potential vulnerabilities are minimized.
- Intrusion Detection and Prevention: Deploy intrusion detection and prevention systems to monitor network traffic for potential threats and quickly respond to any suspicious activities.
- Logging and Monitoring: Enable logging and monitoring of network activities to detect any security breaches or unauthorized access attempts. Regularly review the logs to identify any potential vulnerabilities or incidents.
- Penetration Testing: Conduct regular penetration testing to identify vulnerabilities in the network infrastructure and implement appropriate measures to mitigate those risks.
- Incident Response: Develop and regularly update an incident response plan to effectively respond to any security incidents. This includes defining roles and responsibilities, establishing communication channels, and conducting post-incident analysis.
- Compliance: Ensure that the network security auditing processes align with relevant regulatory requirements and industry best practices.
- Vulnerability Management: Implement a comprehensive vulnerability management program to regularly scan for vulnerabilities, prioritize them based on risk, and promptly remediate any identified issues.
By adhering to these best practices, organizations can enhance the security of their network infrastructure, protect sensitive data, and effectively respond to potential security incidents. Regular network security auditing is crucial for maintaining a strong security posture and reducing the likelihood of successful attacks.
Regular Security Assessments
Regular security assessments are crucial for maintaining the integrity and effectiveness of an organization’s network security. By conducting these assessments on a consistent basis, businesses can proactively identify and address any vulnerabilities in their network infrastructure, reducing the risk of a security incident.
One key aspect of regular security assessments is authentication and authorization. It is important to verify the identity of users accessing network resources and ensure that they have the appropriate level of access. By implementing strong authentication methods and regularly reviewing user permissions, organizations can prevent unauthorized access and mitigate security risks.
Penetration testing is another crucial component of regular security assessments. Organizations can employ ethical hackers to simulate real-world attacks and identify potential vulnerabilities in their network. This proactive approach allows businesses to patch vulnerabilities before malicious actors can exploit them, enhancing overall network security.
Regular security assessments also involve monitoring and detection mechanisms. By implementing robust security monitoring solutions, organizations can identify potential network intrusions and take prompt action to mitigate risks. This includes monitoring firewall logs, analyzing network traffic, and implementing intrusion detection systems.
Compliance is an integral part of regular security assessments. Businesses must ensure they adhere to relevant industry regulations and standards, such as the General Data Protection Regulation (GDPR) or the Payment Card Industry Data Security Standard (PCI DSS). Regular security assessments help businesses evaluate their compliance levels and implement necessary measures to meet these requirements.
Regular security assessments also involve risk analysis and incident response planning. By continuously assessing potential risks, businesses can identify areas of vulnerability and implement appropriate security controls. Additionally, incident response plans are essential for effectively addressing potential security breaches and minimizing their impact on network operations.
In conclusion, regular security assessments are crucial for maintaining a strong and effective network security posture. By conducting authentication and authorization checks, performing penetration testing, investing in monitoring and detection mechanisms, ensuring compliance, and analyzing risks, organizations can strengthen their network security and protect sensitive data from potential threats.
Implementing Strong Authentication
Strong authentication is crucial in ensuring the security of a network and protecting against unauthorized access. By implementing effective authentication measures, organizations can minimize the risk of data breaches, unauthorized access, and potential network vulnerabilities.
Authentication involves verifying the identity of users and devices attempting to access a network or its resources. It is a vital component of network security as it ensures that only authorized individuals or devices can gain access to sensitive information.
To implement strong authentication measures, organizations should consider the following best practices:
- Multifactor authentication: Implementing a combination of factors, such as passwords, biometrics, smart cards, or tokens, enhances the security of the authentication process. This approach significantly reduces the risk of unauthorized access.
- Access controls: Implementing strict access controls ensures that only authorized users have the necessary permissions to access specific resources or perform certain actions. This helps prevent unauthorized access attempts and reduces the risk of data breaches.
- Audit logging and analysis: Regularly auditing and analyzing authentication logs helps to detect any suspicious activities or potential security incidents. This enables organizations to identify vulnerabilities or unauthorized access attempts and take appropriate actions to mitigate risks.
- Incident response and detection: Having an incident response plan in place helps organizations to effectively respond to security incidents and minimize the impact. Regularly monitoring and detecting any abnormalities in authentication processes enables timely response and mitigation.
- Compliance and risk assessment: Regular compliance audits and risk assessments help organizations identify any weaknesses or vulnerabilities in the authentication process. This ensures that necessary measures are taken to address these issues and maintain a high level of security.
- Intrusion prevention: Utilizing intrusion prevention systems and firewalls helps protect against unauthorized access attempts and network intrusions. These security measures act as a barrier between the network and potential threats, enhancing the overall security posture.
- Penetration testing: Regularly conducting penetration tests helps evaluate the security of the authentication system. By simulating real-world attacks, organizations can identify any weaknesses or vulnerabilities and proactively address them.
Implementing strong authentication is essential for organizations to safeguard their networks and protect sensitive data from unauthorized access. By following best practices and employing appropriate security controls, organizations can significantly enhance their overall network security posture and reduce the risk of data breaches and unauthorized access.
Monitoring Network Traffic
Monitoring network traffic is a critical component of ensuring the security and compliance of an organization’s data. By analyzing network traffic, IT professionals can detect and respond to potential intrusion attempts, incidents, and vulnerabilities.
One of the key tools for monitoring network traffic is a firewall. Firewalls act as a barrier between an organization’s internal network and external networks, filtering and monitoring incoming and outgoing traffic. They can detect and prevent unauthorized access, as well as identify and block suspicious activity.
In addition to firewalls, security monitoring systems play an important role in analyzing network traffic. These systems collect and analyze data from various sources, such as logs and network devices, to identify potential threats and vulnerabilities. They can detect patterns and anomalies in network traffic, allowing for early detection and response to security incidents.
Authentication and access controls are also crucial for monitoring network traffic. By implementing strong authentication mechanisms, such as two-factor authentication, organizations can ensure that only authorized individuals have access to the network. Access controls can limit the privileges of users and enforce compliance with security policies.
Network traffic monitoring should also include regular auditing and assessment of the network’s security controls. Audits can identify weaknesses and vulnerabilities in the network, allowing IT professionals to take corrective actions. Penetration testing can be conducted to simulate real-world attacks and test the effectiveness of security measures.
Logging network traffic is another important aspect of monitoring. By keeping detailed logs of network activity, organizations can track and analyze events, helping with incident response and forensic investigations. Logs can provide valuable information for identifying potential intrusions, detecting insider threats, and assessing the overall security posture of the network.
Overall, monitoring network traffic is an essential part of ensuring the security and integrity of an organization’s data. By using a combination of tools, such as firewalls, security monitoring systems, authentication mechanisms, and audits, organizations can detect and respond to potential threats and vulnerabilities in a timely manner.
Strategies for Ensuring Data Protection
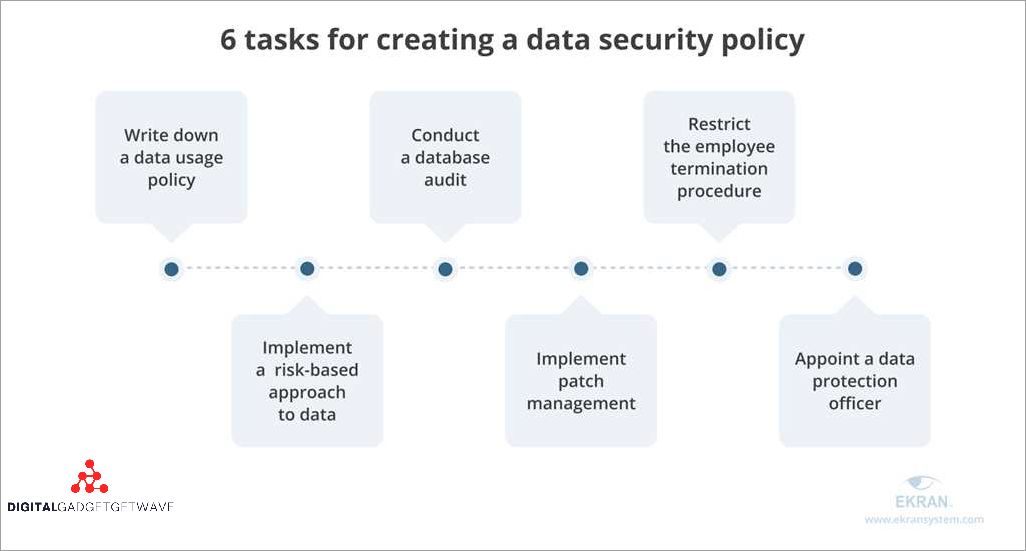
1. Conduct Regular Audits: It is important to regularly review and evaluate the security measures in place to protect sensitive data. Audits can help identify any vulnerabilities or weaknesses in the network and allow for prompt remediation.
2. Perform Penetration Testing: Penetration testing involves simulating real-world cyber attacks to identify any weaknesses in the network defenses. This can help detect potential vulnerabilities and ensure that the appropriate safeguards are in place.
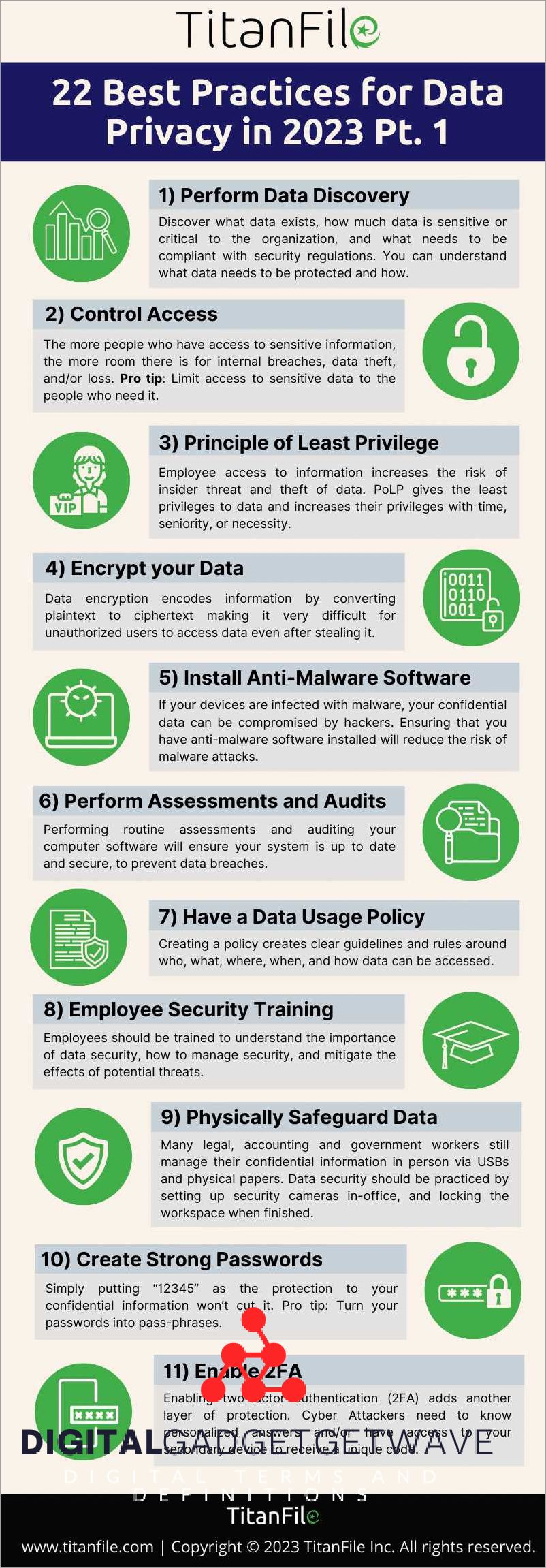
3. Implement Strict Authorization and Access Controls: Controlling access to sensitive data is crucial in ensuring data protection. Implementing strong authentication mechanisms and granting access based on the principle of least privilege can help prevent unauthorized access to critical information.
4. Monitor Network Traffic: Continuous monitoring of network traffic can help identify any suspicious activities or anomalies that may indicate a security breach. Employing intrusion detection and prevention systems, as well as firewall technology, can help detect and prevent unauthorized access to the network.
5. Perform Regular Vulnerability Assessments: Conducting regular vulnerability assessments can help identify and prioritize potential security risks. By systematically identifying and addressing vulnerabilities, organizations can minimize the likelihood of a security incident.
6. Implement Logging and Analysis: Logging network activities and analyzing the collected data can provide insights into potential security threats. By identifying patterns and trends, organizations can proactively detect and respond to potential security incidents.
7. Ensure Compliance with Security Standards: Adhering to industry-specific security standards and regulations is vital in ensuring data protection. Regularly reviewing and updating security policies and procedures can help maintain compliance and mitigate security risks.
8. Establish an Incident Response Plan: Having a well-defined incident response plan is essential in handling security incidents effectively. This plan should outline the steps to be taken in the event of a security breach and should include procedures for containing, investigating, and recovering from the incident.
9. Educate Employees on Security Best Practices: Human error is a common cause of security incidents. Providing regular training and awareness programs on security best practices can help employees understand their responsibilities in protecting data and minimize the risk of unintentional data breaches.
10. Regularly Update Security Controls: Keeping security controls up to date is crucial in staying ahead of evolving cyber threats. Implementing regular patch management and updating software and hardware can help ensure that the network is protected against known vulnerabilities.
Encrypting Data
Encrypting data is a critical security measure to protect sensitive information from unauthorized access and potential risks of data breaches. It is an essential component of any comprehensive network security strategy and plays a crucial role in ensuring the confidentiality and integrity of data.
As part of a network security audit, it is necessary to conduct a thorough analysis of the encryption methods and techniques used to safeguard data. This includes assessing the strength of encryption algorithms, key management practices, and the overall encryption process implemented within the network infrastructure.
Intrusion detection and vulnerability assessments should also include an evaluation of encryption controls to identify any weaknesses or vulnerabilities that could potentially compromise the security of the data. This helps organizations identify and implement necessary security measures to mitigate the risks associated with unauthorized access to encrypted data.
Encryption is particularly important for securing data during transit, such as data exchanges between different network components or data transmitted over the internet. Implementing strong encryption protocols, such as SSL/TLS, ensures that data remains protected during transmission and significantly reduces the risk of interception or eavesdropping.
Furthermore, encryption plays a vital role in compliance efforts, as many industry regulations and data protection laws require organizations to implement appropriate security measures to safeguard sensitive information. Encrypting data not only helps organizations comply with these requirements but also enhances overall data security posture.
Proper authentication and access controls, such as strong passwords, two-factor authentication, and role-based access controls, should accompany encryption efforts to ensure that only authorized individuals can decrypt and access encrypted data. This helps prevent unauthorized individuals from gaining access to sensitive information.
In the event of a security incident, encryption provides an additional layer of protection by reducing the impact of data breaches. Even if an attacker gains unauthorized access to encrypted data, they would still need to decrypt the information, which can be a significantly more challenging task.
Monitoring and logging encryption activities can also aid in incident response and post-incident analysis. Network security teams can review encryption logs to identify any anomalies or suspicious activities that may indicate a security breach or attempted unauthorized access to encrypted data. Additionally, encrypting data stored on physical devices, such as hard drives or portable storage media, further strengthens data protection.
In conclusion, encrypting data is a crucial aspect of network security and data protection. It helps mitigate the risk of data breaches, ensures compliance with regulations, and enhances overall network security posture. By implementing robust encryption methods and practices, organizations can safeguard sensitive information and maintain the confidentiality and integrity of data.
Backing Up Data
Backing up data is an essential component of ensuring data protection in network security. In the event of a security breach, such as a unauthorized access or intrusion, having a reliable backup system in place can be the most effective response to mitigate the impact of the incident.
Regularly scheduled backups enable organizations to quickly recover their data and restore normal operations after a security incident. Access controls should be implemented to limit the authorization required to perform backups, ensuring that only authorized personnel are able to access and manipulate backup data.
Logging and monitoring systems should be in place to detect any potential incidents or unauthorized access attempts. These systems can provide valuable audit trails and help identify any security vulnerabilities that need to be addressed. Moreover, a penetration test or security assessment can be conducted regularly to evaluate the effectiveness of the backup system and identify any potential risks or weaknesses.
When backing up data, organizations should consider the use of encryption and authentication to protect the confidentiality and integrity of the data. This involves using strong encryption algorithms and authentication protocols to prevent unauthorized access to the backup data. Additionally, a firewall can be implemented to further safeguard the backup system from external threats.
In the event of an incident, having a well-documented incident response plan is crucial. This plan should outline the steps to be taken in the event of a security breach, including the restoration of data from backups. Regular testing and analysis of the backup system should be conducted to ensure its reliability and effectiveness.
Finally, compliance with industry standards and regulations is essential when it comes to backing up data. Organizations should ensure that their backup systems adhere to relevant standards and regulations, such as the General Data Protection Regulation (GDPR) or the Payment Card Industry Data Security Standard (PCI DSS). This includes implementing appropriate controls, conducting regular risk assessments, and maintaining documentation of backup procedures and processes.
FAQ about topic “Auditing Network Security: Best Practices and Strategies for Ensuring Data Protection”
What are the best practices for auditing network security?
There are several best practices for auditing network security. First, it is important to regularly perform vulnerability assessments and penetration tests to identify any weaknesses in the network. Second, monitoring network traffic and activity logs can help detect any unauthorized access or suspicious behavior. Third, implementing strong access controls, such as multi-factor authentication, can prevent unauthorized users from accessing the network. Additionally, keeping software and firmware up to date, encrypting sensitive data, and regularly backing up data are also important best practices for auditing network security.
How can I ensure data protection in my network?
To ensure data protection in your network, there are several strategies you can implement. First, you should use strong encryption algorithms to secure sensitive data both in transit and at rest. Second, implementing access controls, such as role-based access control, can ensure that only authorized users have access to sensitive data. Third, regularly backing up data and storing backups in a secure location can protect against data loss and enable recovery in case of a security breach. Finally, monitoring network traffic and activity logs can help detect any unauthorized access or suspicious behavior that could compromise data security.
What are the risks of not auditing network security?
The risks of not auditing network security can be severe. Without auditing, organizations may not be aware of vulnerabilities in their network, making them an easy target for cyberattacks. This can lead to unauthorized access, data breaches, and loss of confidential information. Additionally, without auditing, organizations may not be able to detect insider threats or malicious activity within their network, allowing these threats to go unnoticed and potentially cause significant damage. Overall, not auditing network security can result in financial losses, reputation damage, and legal consequences.
How often should network security audits be performed?
The frequency of network security audits depends on several factors, such as the size of the network, the industry regulations, and the organization’s risk appetite. Generally, it is recommended to perform network security audits at least once a year. However, organizations in high-risk industries or with large networks may need more frequent audits, such as quarterly or monthly. Additionally, network security audits should also be conducted after any major changes or upgrades to the network infrastructure or security controls.
What are the common challenges faced in auditing network security?
Auditing network security can present several challenges. One common challenge is the complexity of network infrastructure, especially in large organizations. Auditors need to understand the network topology, configurations, and security controls in order to effectively assess the security posture. Another challenge is the constant evolution of cybersecurity threats and technologies. Auditors need to stay up to date with the latest attack techniques and security best practices. Limited resources and budget constraints can also pose challenges in terms of conducting comprehensive audits and implementing necessary security measures. Finally, getting buy-in from stakeholders and ensuring cooperation from different departments within the organization can be another hurdle in auditing network security.

