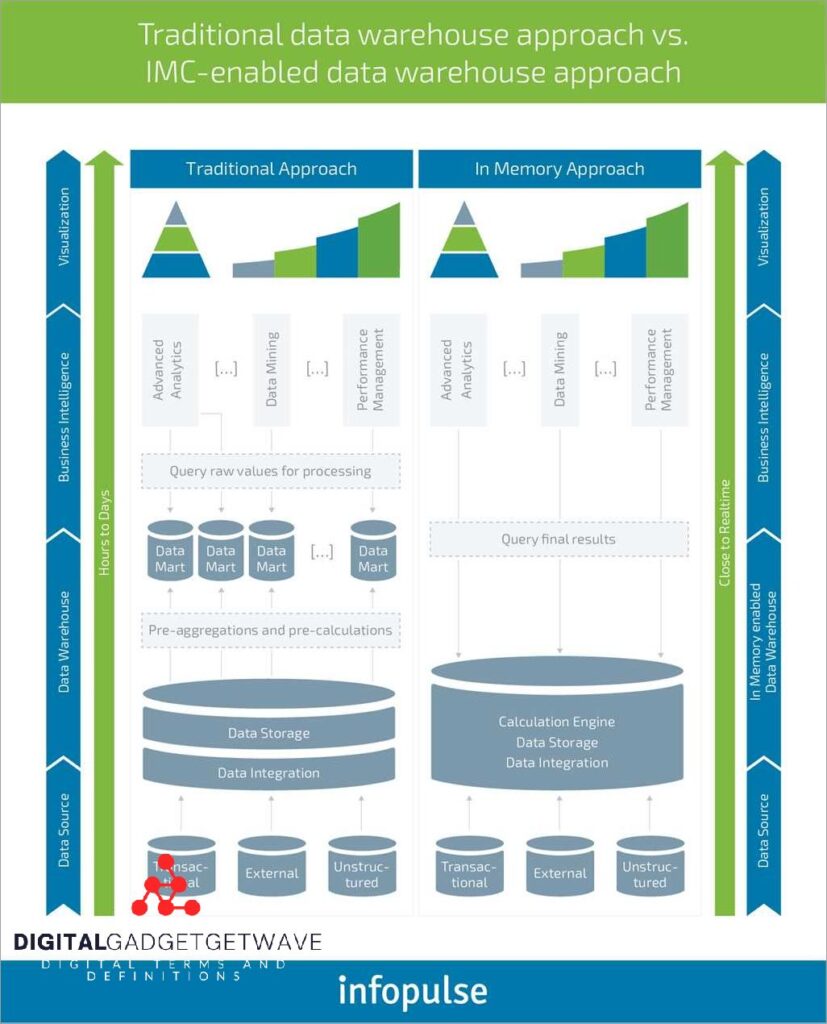
In Memory Analytics: Accelerating Data Insights
With the increasing amount of data being generated in today’s digital world, businesses are constantly looking for ways to analyze and derive valuable insights from this massive pool of information. This is where in-memory analytics comes into play. In-memory analytics is a high-performance data processing platform that allows businesses to process and analyze big data ...