In our rapidly evolving digital landscape, a robust and reliable architecture is essential for organizations to leverage the full potential of technology. Data-centered architecture offers a groundbreaking approach that focuses on maximizing efficiency and security, enabling companies to stay ahead in today’s highly competitive market.
With the growing adoption of cloud computing, analytics, and automation, data-centered architecture is becoming increasingly crucial. By harnessing the power of virtualization and networking, this architecture ensures seamless scalability and flexibility. This allows organizations to rapidly adapt to changing business needs and achieve optimal performance across various environments.
Efficiency and reliability are two key pillars of data-centered architecture. By centralizing data storage and management, organizations can optimize their operations and streamline processes. This approach also enhances security, as sensitive information remains protected and trustworthy within a single, resilient framework.
Integration plays a pivotal role in data-centered architecture, enabling seamless communication and collaboration between different systems and applications. This fosters agility and enables organizations to harness the full potential of their data, driving innovation and informed decision-making. With a data-centered architecture, organizations can unlock the true value of their data and gain a competitive edge in today’s rapidly changing landscape.
Contents
- 1 Data-Centered Architecture
- 2 Maximizing Efficiency and Security
- 3 FAQ about topic “Data-Centered Architecture: Maximizing Efficiency and Security”
- 4 What is data-centered architecture?
- 5 How can data-centered architecture maximize efficiency?
- 6 What are the key benefits of implementing data-centered architecture?
- 7 What are the potential challenges of adopting data-centered architecture?
- 8 How does data-centered architecture enhance data security?
Data-Centered Architecture
Data-Centered Architecture is a fundamental approach to organizing and managing vast amounts of data within an organization. It focuses on the architecture, integration, and flexibility of systems and technologies to optimize performance, efficiency, and security. By leveraging virtualization and cloud technologies, data-centered architecture enables organizations to build resilient and agile infrastructures that can handle the vast amounts of data generated in today’s digital world.
Data-centered architecture facilitates the collection, storage, processing, and analysis of data by providing a trustworthy and secure environment. With robust networking and automation capabilities, organizations can ensure the seamless flow of data between systems and applications. The scalability of data-centered architecture allows organizations to adapt and expand their infrastructure as data volumes grow, without compromising performance or security.
One of the key benefits of data-centered architecture is the ability to leverage advanced analytics capabilities. By utilizing sophisticated algorithms and data mining techniques, organizations can extract valuable insights and make data-driven decisions. This optimization of data utilization leads to improved efficiency and competitive advantage.
In conclusion, data-centered architecture is a comprehensive approach to managing data within an organization. It provides the necessary infrastructure, technologies, and processes to ensure efficient and secure data handling. By leveraging virtualization, cloud, and automation technologies, organizations can build resilient and agile data infrastructures that support advanced analytics and drive business growth.
Maximizing Efficiency and Security
In today’s data-driven world, efficiency and security are paramount. Organizations need reliable and secure systems to handle large volumes of data and ensure seamless networking. An agile and optimized data-centered architecture can provide the foundation for achieving these goals.
The cloud has revolutionized the way data is stored and managed. By leveraging cloud technology, organizations can enhance security measures, enable real-time analytics, and facilitate integration across different platforms. The flexibility and scalability offered by the cloud allow businesses to adapt and grow without compromising the efficiency and security of their data.
Data-centered architecture helps organizations build resilient and trustworthy systems. Virtualization and automation play a crucial role in achieving this. By virtualizing resources, organizations can optimize the use of hardware and improve efficiency. Automation streamlines processes, reduces human error, and enhances security by eliminating manual intervention.
Efficiency can also be maximized through data-centered architecture by focusing on optimization techniques. Analyzing data patterns and trends can help identify areas where improvements can be made. By implementing efficient algorithms and strategies, organizations can optimize storage, processing time, and overall system performance.
Security is a fundamental aspect of data-centered architecture. Robust security measures, such as encryption, access controls, and intrusion detection systems, help safeguard sensitive information from unauthorized access. Regular security audits and updates ensure the system remains protected against emerging threats.
In conclusion, a well-designed data-centered architecture is crucial for maximizing efficiency and security. It leverages cloud technology, enables analytics, promotes integration, and employs virtualization and automation. By prioritizing reliability, scalability, and flexibility, organizations can build resilient and trustworthy systems that efficiently handle their data while maintaining the highest level of security.
What is Data-Centered Architecture?

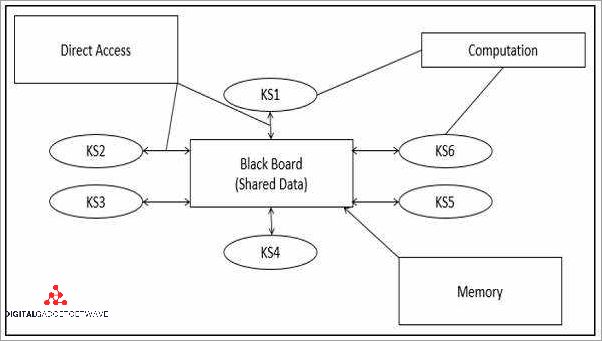
Data-Centered Architecture is a networking and integration approach that focuses on creating a trustworthy and efficient system for managing, storing, and processing data. The architecture leverages cloud technology to provide flexibility, optimization, and resilience to meet the performance and reliability requirements of modern businesses.
An agile and scalable architecture, Data-Centered Architecture enables automation and virtualization, allowing quick deployment and easy management of resources. By centralizing data and analytics, it enables organizations to make informed decisions and gain valuable insights to drive business growth.
Security is a critical aspect of Data-Centered Architecture. It incorporates robust security measures to protect data from unauthorized access, ensuring confidentiality, integrity, and availability. The architecture employs advanced technologies and best practices to secure data at various levels and prevent data breaches.
Data-Centered Architecture provides efficient data processing and storage capabilities, allowing organizations to optimize resource usage and improve operational efficiency. It enables seamless scalability, ensuring that the system can handle increasing data volumes and user demands without compromising performance.
In conclusion, Data-Centered Architecture is a comprehensive approach that combines the power of technology, analytics, and security to create a highly efficient and secure environment for managing and processing data. It offers organizations the flexibility, scalability, and reliability needed to stay ahead in today’s data-driven world.
The Importance of Efficiency
In today’s data-centered architecture, efficiency plays a crucial role in achieving optimal performance, scalability, and reliability. With the increasing volume and complexity of data, organizations rely heavily on analytics to gain valuable insights. An efficient data-centered architecture enables organizations to streamline their analytics processes, resulting in faster and more accurate decision-making.
A centered architecture ensures that data is stored, processed, and accessed in a resilient manner. Automation and integration are key components of an efficient architecture. By automating repetitive tasks, organizations can save time and reduce the risk of human error. Integration allows different systems and applications to seamlessly communicate and share data, facilitating efficient retrieval and processing.
Virtualization and cloud technologies enhance efficiency by enabling organizations to optimize their resources. By virtualizing their infrastructure, organizations can consolidate their hardware, leading to cost savings and improved scalability. Cloud services also provide flexibility and enable organizations to quickly scale their resources up or down based on demand.
Efficiency is closely tied to security and trustworthiness. An efficient architecture ensures that data is securely stored and transmitted, minimizing the risk of unauthorized access or data breaches. By optimizing their network architecture, organizations can improve the performance and reliability of their data transfers. They can also implement robust security measures such as encryption and multi-factor authentication to protect their sensitive data.
In conclusion, an efficient data-centered architecture is essential for organizations to effectively leverage their data for informed decision-making. It enables analytics processes to be streamlined, promotes scalability and flexibility, and ensures the security and reliability of data. By optimizing their architecture through automation, integration, virtualization, and security measures, organizations can maximize efficiency and unlock the full potential of their data.
Reducing Costs and Resources

Implementing a data-centered architecture can significantly reduce costs and optimize resource allocation. By utilizing cloud technology, organizations can eliminate the need for excessive hardware and maintenance costs. The cloud provides a scalable and flexible environment for storing, managing, and analyzing large volumes of data, ensuring that resources are allocated efficiently and cost-effectively. Furthermore, the integration of virtualization technology allows for the consolidation of servers, reducing power and cooling requirements.
Networking plays a crucial role in reducing costs and optimizing efficiency in a data-centered architecture. By implementing a reliable and resilient network infrastructure, organizations can ensure high performance and availability of data. This enables efficient data transfer and eliminates costly downtime. Additionally, trustworthy security measures, such as encryption and authentication protocols, can be implemented to safeguard data during transmission and storage.
Efficient data management is a key factor in reducing costs and optimizing resource allocation. Through the use of data analytics, organizations can identify patterns and trends, enabling agile decision-making and resource optimization. By leveraging advanced analytics tools, organizations can gain valuable insights that drive efficiency and cost reduction. Additionally, data integration allows for seamless connectivity between different systems and applications, eliminating redundant processes and reducing resource consumption.
In conclusion, implementing a data-centered architecture can lead to significant cost reduction and resource optimization. By leveraging cloud technology, organizations can minimize hardware costs and efficiently allocate resources. Networking and security measures ensure reliable and secure data transmission and storage. Efficient data management, through analytics and integration, drives agility and reduces resource consumption. By embracing data-centered architecture, organizations can achieve cost savings, improve efficiency, and enhance overall performance.
Optimizing Performance and Scalability
In today’s rapidly changing business landscape, organizations must continuously find ways to optimize performance and scalability in order to stay competitive. One key approach is leveraging cloud technology to enable automation and streamline processes. By utilizing cloud services, organizations can achieve greater efficiency and agility, allowing them to scale resources up or down as needed without the need for significant infrastructure investments.
A data-centered architecture is crucial for optimizing performance and scalability. By placing data at the center of the architecture, organizations can ensure that all processes and systems are built around it, enabling quick and reliable access. This architecture also helps in maintaining data security and privacy, making the organization more trustworthy in the eyes of customers and stakeholders.
Virtualization is another essential component of optimizing performance and scalability. By decoupling software from hardware, organizations can achieve greater flexibility and resource utilization. With virtualization, multiple virtual machines can run on a single physical server, enabling efficient use of resources and better performance. Additionally, virtualization allows for easy migration and backup of virtual machines, enhancing reliability and resilience.
To further optimize performance and scalability, organizations should leverage analytics and optimization techniques. By analyzing data and performance metrics, organizations can identify bottlenecks and areas for improvement. Through optimization, organizations can fine-tune their systems and processes to achieve better performance and scalability. This proactive approach helps in ensuring that systems can handle increasing workloads without sacrificing reliability or user experience.
Networking also plays a crucial role in optimizing performance and scalability. By implementing robust and reliable networking infrastructure, organizations can ensure quick and seamless data transfer between different components of the architecture. This enables efficient communication and collaboration, leading to improved overall performance. Additionally, organizations can leverage technologies like load balancing and content delivery networks to distribute workloads and optimize resource utilization.
In conclusion, optimizing performance and scalability requires a data-centered architecture, virtualization, analytics, optimized networking, and efficient use of cloud technology. By leveraging these approaches, organizations can achieve higher efficiency, reliability, and security while adapting to changing business needs in an agile manner.
The Role of Security

Security plays a crucial role in data-centered architecture, as technology advances and integration with external systems become more prevalent. In order to maintain the reliability and performance of the system, robust security measures must be implemented. This includes secure networking protocols, encryption techniques, and access control mechanisms.
Analytics and automation also play a significant role in enhancing security. By utilizing advanced analytics, security teams can detect and respond to potential threats more efficiently. Automation can be used to quickly remediate security incidents and minimize their impact on the system.
Virtualization and optimization are key components of a secure data-centered architecture. By virtualizing resources, such as servers and storage, organizations can create isolated environments for sensitive data. This ensures that in the event of a breach, the impact is limited to a specific virtualized instance rather than the entire system. Optimization techniques, such as load balancing and resource allocation, can also improve security by preventing resource exhaustion attacks.
Trustworthy and resilient architecture is important for securing data in a data-centered environment. Implementing redundancy and failover mechanisms ensures that critical systems and data are available even in the event of hardware or software failures. Flexible architecture allows for quick adaptation to changing security threats, ensuring that the system remains secure over time.
In conclusion, security is a vital aspect of data-centered architecture, as it ensures the confidentiality, integrity, and availability of data. By implementing robust security measures, organizations can maximize efficiency, scalability, and performance while minimizing the risks associated with data breaches or unauthorized access.
Ensuring the security of data is a crucial aspect of any data-centered architecture. Unauthorized access to sensitive information can have severe consequences, including financial loss, reputational damage, and legal issues. Therefore, it is essential to implement robust security measures to protect data from unauthorized access.
A key component of protecting data is establishing a secure networking infrastructure. This involves implementing firewalls, intrusion detection systems, and encryption protocols to prevent unauthorized users from gaining access to data through network vulnerabilities.
Efficiency and scalability are also important factors in protecting data. By adopting cloud-based solutions, organizations can benefit from a resilient and agile data architecture that can quickly scale to accommodate increasing data volumes and user demands. Virtualization technology can further enhance security by isolating sensitive data and applications from unauthorized access.
To ensure data security, it is essential to implement trustworthy authentication and authorization mechanisms. Multi-factor authentication, strong password policies, and role-based access control can help prevent unauthorized users from gaining privileged access to sensitive information. Regularly auditing user access and enforcing data access policies can further fortify security.
Data encryption is another critical aspect of protecting data. By encrypting data at rest and in transit, organizations can enhance the confidentiality and integrity of sensitive information. Additionally, data masking and tokenization techniques can be used to protect data while still allowing for meaningful analytics and integration with other systems.
Flexibility and automation play a crucial role in data security as well. By integrating security measures into the data architecture, organizations can automate security controls and monitoring processes. This ensures that data remains protected without relying solely on manual interventions, reducing the risk of human errors and increasing overall security efficiency.
Mitigating Risks and Vulnerabilities

In data-centered architecture, mitigating risks and vulnerabilities is crucial to ensure efficient and secure operations. By implementing trustworthy technologies and practices, organizations can optimize their systems for maximum performance and flexibility while minimizing potential vulnerabilities.
One of the key strategies for mitigating risks is through the use of resilient architecture. This involves leveraging virtualization techniques to isolate and contain potential threats, ensuring that even if one component is compromised, the rest of the system remains secure.
Scalability and integration are also essential considerations when mitigating risks and vulnerabilities. By designing systems with scalability in mind, organizations can adapt to changing needs and seamlessly integrate new technologies while maintaining the security and efficiency of their data.
Technological advancements, such as automation and cloud computing, play a significant role in mitigating risks and vulnerabilities. Automation allows for streamlined processes and reduces human error, while the cloud provides secure storage and backup for critical data.
An agile and reliable networking infrastructure is another critical aspect of risk mitigation. By leveraging advanced networking technologies, organizations can ensure efficient and secure data transfer, minimizing the risk of unauthorized access or data breaches.
Overall, a data-centered architecture focused on mitigating risks and vulnerabilities should prioritize efficiency, security, and reliability. By employing trustworthy technologies and practices, optimizing systems for flexibility and scalability, and leveraging advanced networking and automation capabilities, organizations can ensure the protection and integrity of their data.
FAQ about topic “Data-Centered Architecture: Maximizing Efficiency and Security”
What is data-centered architecture?
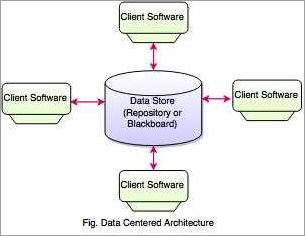
Data-centered architecture refers to a system design approach that focuses on organizing and managing data as the primary component. It involves structuring data in a way that allows easy access, retrieval, and manipulation. In this architecture, data is treated as a valuable asset, and all other components, such as applications and services, revolve around it.
How can data-centered architecture maximize efficiency?
Data-centered architecture can maximize efficiency by providing a centralized and standardized approach to managing and accessing data. By structuring data in a consistent manner, it becomes easier to search, analyze, and process. This reduces duplication, improves data quality, and enhances overall system performance. Additionally, data-centered architecture enables efficient data integration across multiple systems and supports scalability as businesses grow.
What are the key benefits of implementing data-centered architecture?
Data-centered architecture offers several key benefits, including improved data quality and consistency. By centralizing data management, organizations can enforce data standards and rules, reducing errors and inconsistencies. Additionally, data-centered architecture enhances data security by ensuring access control and encryption measures are implemented consistently. It also enables easier data sharing and integration, leading to improved collaboration and decision-making across the organization.
What are the potential challenges of adopting data-centered architecture?
While data-centered architecture offers many benefits, there are some potential challenges to consider. One challenge is the initial cost and effort involved in transitioning to this architecture. Organizations may need to invest in new infrastructure, tools, and training to effectively implement and manage data-centered systems. Another challenge is ensuring data privacy and compliance with regulations, as data is centralized and may be accessed by multiple applications. It’s important to establish robust security measures and procedures to mitigate these risks.
How does data-centered architecture enhance data security?
Data-centered architecture enhances data security through various mechanisms. Firstly, by centralizing data management, it becomes easier to implement access control policies and authentication mechanisms across the organization. Secondly, data encryption can be applied consistently, ensuring data remains protected throughout its lifecycle. Additionally, data-centered architecture allows for better monitoring and auditing of data access, helping detect and respond to any security breaches or unauthorized activities promptly. Overall, this architecture provides a holistic approach to data security.

