The digital revolution has brought significant advancements in telephony and communication networks. However, with these developments has also come new vulnerabilities that can be exploited by malicious actors. One such group of individuals are known as phreakers, who engage in the practice of phreaking – the manipulation of telephone systems and signals.
Phreaking, a term coined in the 1970s, involves a combination of technical expertise and an understanding of the inner workings of telephone networks. Phreakers exploit weaknesses in the network infrastructure to make illicit phone calls, bypass billing systems, or gain unauthorized access to sensitive information. These individuals utilize their knowledge of telephony technology to create and execute various techniques to manipulate the phone system to their advantage.
While some phreakers engage in phreaking as a form of prank or self-amusement, others pursue it as a means of cybercrime and fraud. With advancements in technology, phreaking techniques have evolved to include wiretapping, spoofing, and signal manipulation. These techniques enable phreakers to intercept or redirect phone calls, manipulate caller ID information, and even create counterfeit signals to gain unauthorized access.
The history of phreaking can be traced back to the early days of the telephone network, where individuals discovered the vulnerabilities of the system and explored ways to exploit them. What started as a curiosity quickly evolved into a sophisticated art form practiced by individuals with a deep understanding of the inner workings of the telephone network. Today, phreaking continues to be a concern for network security as phreakers adapt and develop new techniques to exploit the vulnerabilities in telephony systems.
Contents
- 1 Understanding the World of Phreaking
- 2 Exploring the Origins and Techniques of Phreakers
- 3 The Origins of Phreaking
- 4 Techniques Used by Phreakers
- 5 Legal and Ethical Considerations
- 6 The Impact of Phreaking on Society
- 7 FAQ about topic “Understanding the World of Phreaking: Exploring the Origins and Techniques of Phreakers”
- 8 What is phreaking?
- 9 How did phreaking begin?
- 10 What techniques do phreakers use?
- 11 Is phreaking illegal?
- 12 Has phreaking evolved with advancements in technology?
Understanding the World of Phreaking
Phreaking refers to the act of exploring and manipulating technology and signals in the telecommunication network. It involves exploiting vulnerabilities in the telephone system to make free calls, manipulate billing systems, and even wiretap conversations.
Phreaking has a long history that dates back to the 1960s when a group of hackers discovered that certain tones could be used to control the telephone network. These individuals, known as phreakers, developed techniques to bypass security measures and access restricted services.
The motivations behind phreaking can vary. Some phreakers engage in this activity as a form of prank or curiosity, while others seek to commit fraud for financial gain. More recently, phreaking has evolved into a form of cybercrime, where phreakers exploit the vulnerabilities in telephone and telecommunication networks for malicious purposes.
Phreaking techniques often involve the manipulation of digital signals, such as using specific tones or frequencies to gain access to network features or make unauthorized calls. Phreakers have also discovered ways to bypass security systems and gain control over various aspects of the telephone network.
Understanding and addressing the security vulnerabilities in telecommunication networks is crucial to prevent phreaking attacks. Telephone and network operators constantly work to identify and patch vulnerabilities to protect their systems from phreakers and other malicious hackers.
In conclusion, phreaking is a practice that involves exploring and manipulating the technology and signals in the telecommunication network. Phreakers exploit vulnerabilities in the system to gain unauthorized access, manipulate billing systems, and even wiretap conversations. The evolution of phreaking as a cybercrime highlights the need for strong security measures to protect telephone and telecommunication networks from these malicious activities.
Exploring the Origins and Techniques of Phreakers
A phreaker is a type of hacker who specializes in exploring and exploiting vulnerabilities in telecommunication systems. They manipulate the signal and exploit weaknesses in the phone network to make free calls, eavesdrop on conversations, or engage in other acts of mischief or fraud.
Phreaking originated in the early days of telephony, when hackers discovered that certain tones and signals could be used to manipulate the telephone system. They would use simple devices like blue boxes to imitate the signaling tones used by the phone system, allowing them to make calls without being detected or charged.
Over time, phreakers became more sophisticated in their techniques. They would wiretap phone lines to listen in on conversations, use sophisticated computer programs and algorithms to find vulnerabilities in the phone network, and even hack into the network to gain unauthorized access.
This cybercrime became a cat-and-mouse game between phreakers and the authorities. Telecommunication companies had to constantly update their security measures to prevent phreakers from exploiting their systems. However, phreakers always found new ways to manipulate the technology and stay one step ahead.
Phreaking has had a significant impact on the development of security measures in telecommunication systems. The vulnerabilities discovered by phreakers have led to the improvement of network security, as companies have had to constantly adapt and find solutions to protect their systems.
While the intentions of phreakers may vary, ranging from harmless pranks to malicious fraud, the techniques they use continue to evolve alongside the advancements in technology. Phreaking serves as a reminder of the importance of staying vigilant and continuously updating our security practices to protect our communication networks.
The Origins of Phreaking
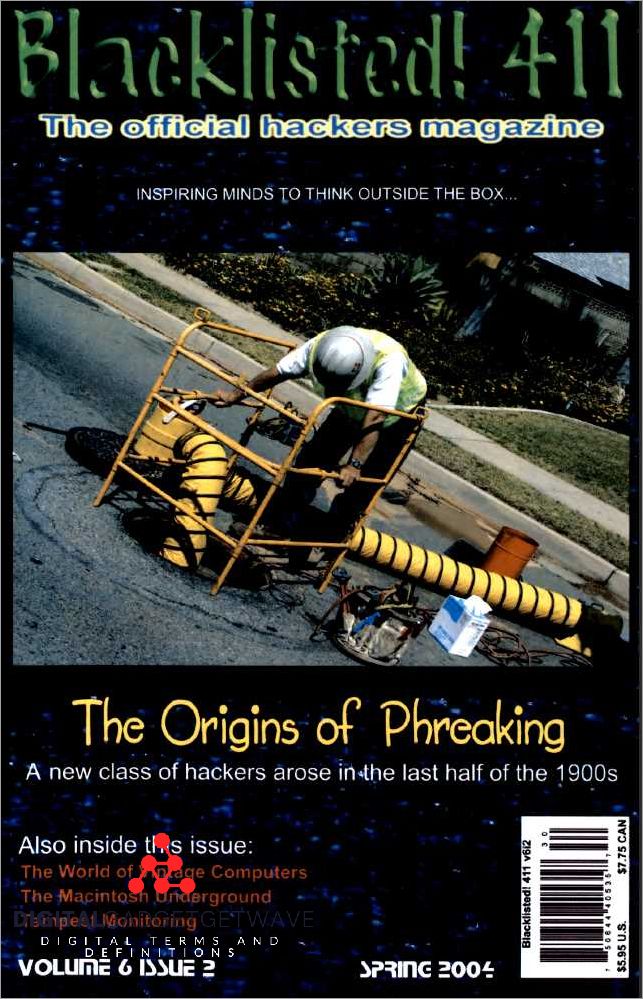
The phenomenon of phreaking emerged in the mid-20th century, when early hackers and technology enthusiasts began to explore the security vulnerabilities of the telephone network. Phreakers, as they came to be known, realized that they could manipulate the signal and digital technology used in telephony to exploit the network’s vulnerabilities.
The origins of phreaking can be traced back to the 1960s, when young hackers like John Draper, also known as Captain Crunch, explored and experimented with the phone system. They discovered that certain tones and combinations of frequencies could be used to trick the network into granting them free calls or access to restricted lines.
Phreakers went beyond the pranks and mischief commonly associated with their activities. They pioneered the exploration of telecommunication systems, examining the inner workings of the phone network and finding ways to manipulate it. This early form of hacking laid the foundation for future generations of cybercriminals to exploit and manipulate communication networks for various purposes, including fraud and other forms of cybercrime.
Phreaking was not limited to wiretapping or intercepting telephone calls. Phreakers also discovered vulnerabilities in the network infrastructure, such as weak points in the signaling systems, which allowed them to gain unauthorized access to various telephony services.
This exploration of the telephone network ultimately led to the development of the modern hacker culture, with phreakers playing a crucial role in shaping the understanding of network security and vulnerabilities. Today, phreaking has evolved into a more sophisticated form of cybercrime, but its origins remain a significant part of the history of hacker culture and the exploration of communication technology.
The Early Days of Phreaking
In the early days of telephony, communication systems were vulnerable to manipulation, leading to the birth of phreaking. Phreaking, a term coined by hackers, refers to the exploration and exploitation of telecommunication networks for various purposes.
Phreakers, a group of skilled hackers, discovered security vulnerabilities in the telephone system, allowing them to manipulate signals and make free phone calls. They explored the digital landscape of telephony, finding weaknesses in the network infrastructure that allowed them to bypass billing systems and make unauthorized calls.
These early phreakers were pioneers in the world of telecommunication fraud, using their knowledge of technology and the telephone system to exploit loopholes for personal gain. They uncovered ways to wiretap phone lines, clone telephone cards, and even create their own devices to mimic signals and manipulate the system.
What started as a prank among hackers quickly turned into a form of cybercrime, as phreakers realized the potential for financial gain by exploiting the vulnerabilities in the telecommunication network. They formed underground communities and shared their knowledge, developing new techniques and pushing the boundaries of what was possible.
Ultimately, the early days of phreaking laid the foundation for modern-day hacking and cybercrime. The techniques and tactics developed by these early phreakers paved the way for future hackers to exploit vulnerabilities in communication systems and manipulate technology for personal gain.
Influential Figures in Phreaking History
Phreaking is a subculture within the world of cybercrime that revolves around manipulating and exploiting telecommunication systems for personal gain. Over time, a number of influential figures have emerged in the phreaking community, each contributing to the evolution of this unique form of technology-based fraud.
John Draper, also known as “Captain Crunch,” is one of the most prominent figures in phreaking history. In the 1970s, Draper discovered that a toy whistle found in a cereal box could emit a tone at the same frequency used by telephone switches to indicate an incoming call. By using this “blue box” technique, Draper was able to manipulate the phone system and make free long-distance calls.
Kevin Mitnick, a renowned hacker and phreaker, gained notoriety in the 1980s for his ability to bypass security systems and exploit vulnerabilities in various networks. With his deep understanding of telephony and computer systems, Mitnick was able to wiretap phone lines and gain unauthorized access to sensitive information. His actions led to significant changes in telecommunication security protocols.
Mark Abene, also known as “Phiber Optik,” became a prominent figure in the phreaking community in the 1990s. Abene specialized in exploring the vulnerabilities of the emerging digital telephony networks. He showcased his skills by demonstrating how easy it was to intercept and manipulate digital communication signals, bringing attention to the need for stronger security measures.
Emmanuel Goldstein, founder and editor of the legendary hacker magazine “2600: The Hacker Quarterly,” played an influential role in popularizing phreaking and bringing it to the mainstream. Through his magazine, Goldstein provided a platform for phreakers and hackers to share their knowledge and experiences, fostering a sense of community and pushing the boundaries of technology.
These influential figures, among many others, have significantly shaped the history of phreaking and made lasting contributions to the understanding of telecommunication systems, vulnerabilities, and the importance of security in the digital age.
Techniques Used by Phreakers

Phreaking is a term used to describe the activity of exploring and manipulating the telecommunication systems, particularly the telephone networks. Phreakers, who are essentially hackers specialized in telephony, use various techniques to exploit vulnerabilities in the telephony infrastructure for their own purposes.
One common technique used by phreakers is wiretapping. By tapping into telephone lines and intercepting the signals, phreakers can eavesdrop on conversations or gain unauthorized access to services. This can be done physically by connecting wires to the telephone lines, or digitally by exploiting vulnerabilities in the network.
Another technique used by phreakers is the manipulation of the signaling systems used in telecommunication networks. By manipulating the signaling protocols, phreakers can bypass security measures and gain unauthorized access to phone services or make fraudulent calls. This can involve spoofing caller IDs, manipulating call routing, or exploiting weaknesses in the encryption algorithms.
Phreakers also use various techniques to exploit the digital nature of modern telephony. For example, they may use software programs to scan telephone networks for vulnerable systems or to automate the process of dialing and exploring different phone numbers. This allows them to quickly identify and exploit weaknesses in the system.
Furthermore, phreakers may engage in social engineering techniques to gather information or gain unauthorized access to phone services. This can involve impersonating authorized personnel, tricking individuals into revealing sensitive information, or manipulating customer service representatives into granting them access to restricted services.
In conclusion, phreakers use a range of techniques to exploit vulnerabilities in telecommunication systems and manipulate telephone networks. These activities can range from harmless pranks to serious fraud and cybercrime, highlighting the importance of maintaining robust security measures in the evolving world of telecommunication technology.
Phone System Exploits
Phone system exploits refer to the techniques and methods used by phreakers to manipulate and exploit vulnerabilities in the telecommunication network. These exploits can have significant implications for communication security and can be considered a form of cybercrime.
One common exploit used by phreakers is wiretapping, where they intercept and listen to phone conversations without the knowledge or consent of the parties involved. This illegal activity allows hackers to gain unauthorized access to private information and potentially use it for fraudulent activities.
Phreaking, the act of manipulating the telephone network, originally emerged in the 1960s and 1970s when hackers discovered vulnerabilities in the analog telephone system. With the advent of digital technology, these exploits have evolved, allowing hackers to gain control over various aspects of the phone network and manipulate phone signals in a variety of ways.
Security vulnerabilities in the phone system can result from weaknesses in signaling protocols and network infrastructure. These weaknesses can be exploited by phreakers to make unauthorized calls, bypass call restrictions, or even launch attacks on other systems connected to the network.
Phreaking exploits are not always malicious in intent, as some hackers engage in this activity as a form of technological pranks or for the thrill of exploring the limits of telephony technology. However, regardless of the intent, phone system vulnerabilities can have serious consequences for individuals, businesses, and society as a whole.
Efforts to address these vulnerabilities have led to advancements in telecommunication security, such as improved encryption protocols and network monitoring systems. However, as technology continues to evolve, so too do the techniques used by phreakers. It remains essential for telecommunication companies and individuals to stay vigilant and regularly update their security measures to protect against phone system exploits.
Social Engineering
Social engineering is a form of cybercrime that relies on manipulating individuals rather than exploiting technical vulnerabilities in telecommunication systems. It involves the use of psychological tactics to deceive and manipulate people into providing sensitive information or granting unauthorized access to systems.
One common telecommunication-related social engineering technique is known as pretexting. This involves creating a fictional scenario to trick someone into revealing information or performing actions they otherwise wouldn’t. For example, a fraudster might call a telephone company and pretend to be an employee in order to gain access to customer records or wiretap a specific line.
Another social engineering technique is phishing, which is typically carried out through digital communication channels like email or instant messaging. Phishing involves sending fraudulent messages that appear to be from a trusted source, such as a bank or social media platform, with the aim of tricking recipients into revealing sensitive information or downloading malicious software.
Telephony pranks are another form of social engineering that involve manipulating individuals for amusement or entertainment purposes. These pranks often exploit vulnerabilities in communication networks to reroute or spoof phone calls, leading to confusion or distress for the recipient.
To protect against social engineering attacks, it is important to be vigilant and skeptical of unsolicited communication or requests for sensitive information. Organizations should also implement security measures such as multi-factor authentication and employee training programs to educate individuals about the risks and techniques used by social engineers.
Phone Phreaking Tools and Devices
Phone phreaking is the act of manipulating telecommunication systems to exploit vulnerabilities in the telephone network. Phreakers, also known as phone hackers, use various tools and devices to carry out their activities.
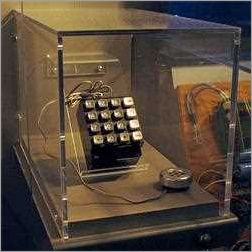
One common tool used by phreakers is the blue box, a device that generates specific tones to mimic the signals used by telephone networks. By playing these tones into a phone receiver, a phreaker can manipulate the network and make free long-distance calls or gain unauthorized access to certain services.
Another device commonly used by phreakers is the red box. This device replicates the tone sent by payphones to indicate that coins have been inserted. By playing this tone into a payphone receiver, a phreaker can trick the system into thinking that payment has been made, allowing them to make free calls.
Phreakers also employ a technique known as call spoofing, which involves manipulating the caller ID system to display a false number. This can be done using a device called a caller ID spoofing box, which allows phreakers to make calls appear to come from a different phone number. This technique is often used in cybercrime activities, such as fraud or identity theft.
In addition to these physical devices, phreakers also utilize software tools to manipulate telephony systems. One such tool is a war dialer, which automatically dials a range of phone numbers to detect vulnerabilities that can be exploited. Another tool is a wiretap device, which intercepts and records phone conversations without the knowledge or consent of the parties involved.
It is important to note that while phone phreaking techniques were originally used for harmless exploration and pranks, they can also be utilized for illegal activities. Phone phreaking falls under the umbrella of cybercrime and is considered illegal in most jurisdictions. The advancements in digital technology and the increasing complexity of telecommunication systems have made it more challenging for phreakers to exploit vulnerabilities in the network, but the threat remains.
Legal and Ethical Considerations
When discussing the world of phreaking, it is important to consider the legal and ethical implications of engaging in activities that involve manipulation of digital communication systems. Phreaking, a term derived from “phone” and “freaking,” refers to the subculture of individuals who specialize in exploring and exploiting the vulnerabilities of telecommunication technology.
One of the key legal considerations is the Wiretap Act, which prohibits the unauthorized interception of electronic communications, including phone signals. Engaging in phreaking activities that involve wiretapping without proper authorization is illegal and can result in severe penalties.
From an ethical standpoint, phreaking raises questions about the potential harm it can cause to individuals and organizations. While some phreakers engage in harmless pranks or exploration, there are instances where the knowledge and techniques obtained through phreaking can be used for malicious purposes, such as fraud or cybercrime.
Telecommunication networks, including telephone systems, rely on security measures to ensure the integrity and confidentiality of communication. Phreakers, by exploiting vulnerabilities in these networks, undermine the trust and security that users place in these systems. This can have far-reaching consequences, both for individuals and for society as a whole.
As technology evolves, so do the techniques used by phreakers. It is crucial for lawmakers and the telecommunications industry to stay vigilant and keep up with these advancements in order to protect the privacy and security of digital communication.
In conclusion, while phreaking may seem like an intriguing and fascinating subculture, it is important to recognize the legal and ethical considerations that come with it. Engaging in phreaking activities without proper authorization is illegal, and the potential harm that can be caused by manipulating telecommunication systems raises important ethical questions. As our reliance on technology continues to grow, it is crucial to prioritize the security and integrity of digital communication networks.
Legal Consequences of Phreaking
Phreaking, a term derived from “phone” and “freaking,” refers to the act of manipulating telecommunication systems to gain unauthorized access or control. While some individuals view phreaking as a harmless prank or exploration of technology, it is important to understand that engaging in phreaking activities can have severe legal consequences.
Phreaking involves exploiting vulnerabilities in the telephony network and manipulating phone signals using digital techniques. These actions can be categorized as cybercrime and fall under the purview of different legal frameworks, including laws governing wiretapping, fraud, and communication security.
Wiretapping, or the interception of communication, is illegal in most jurisdictions without proper authorization. Phreakers who intercept or listen in on telephone conversations can face serious legal penalties, including fines and imprisonment. Such acts violate the privacy rights of individuals and can compromise sensitive information.
Phreaking can also be considered a form of fraud, as phreakers manipulate telecommunication systems to make free calls or exploit billing systems. This can result in financial losses for both individuals and service providers. Engaging in fraudulent activities through phreaking can lead to criminal charges and legal ramifications.
Furthermore, phreaking can be seen as a breach of communication security. Phreakers exploit vulnerabilities in the telecommunication infrastructure, potentially compromising the confidentiality, integrity, and availability of communication networks. This jeopardizes the trust individuals and businesses have in these systems and can result in legal action.
As technology continues to advance, the legal consequences of phreaking have become more severe. Law enforcement agencies and telecommunication companies are actively working to detect and prevent phreaking activities, implementing measures to address network vulnerabilities and prosecute those involved in these illegal activities.
In conclusion, phreaking may seem like a harmless exploration of technology, but it carries significant legal consequences. Individuals engaging in phreaking activities risk facing legal penalties, including fines, imprisonment, and criminal records. It is essential to understand and respect the boundaries of telecommunication systems to ensure a secure and lawful digital environment.
Ethical Debate Surrounding Phreaking
In the world of telecommunication technology, phreaking refers to the manipulation and exploitation of telephone systems to gain unauthorized access and control over signal networks. Although phreakers are often regarded as hackers, the ethical debate surrounding their activities is still a heated topic of discussion.
On one hand, proponents argue that phreaking is a valuable tool for exposing vulnerabilities in telecommunication networks. By uncovering weaknesses, phreakers can help improve the security and effectiveness of these systems. Furthermore, they argue that phreaking is akin to ethical hacking, as it involves testing security measures and finding ways to strengthen them.
On the other hand, critics argue that phreaking is a form of fraud and cybercrime, as it involves unauthorized access to telephone networks. They highlight the potential for financial loss and disruption caused by phreaking activities, as well as the violation of privacy through wiretapping and interception of communication. Phreakers are accused of taking advantage of vulnerabilities for personal gain rather than serving the greater good.
The ethical debate surrounding phreaking also raises questions about the legality of their actions. While some argue that phreaking falls within a gray area of the law, others suggest that it is undoubtedly illegal due to its potential to cause harm and exploit weaknesses in digital security systems. Therefore, the distinction between an innocent prank and a malicious attack by a phreaker is a complex issue that depends on the intent and impact of their actions.
In conclusion, the ethical debate surrounding phreaking revolves around the balance between the potential benefits of exposing vulnerabilities for improving security and the potential harm caused by unauthorized access and manipulation of telephone systems. As technology continues to evolve, the discussion around the ethical boundaries of phreaking will undoubtedly continue to evolve as well.
The Impact of Phreaking on Society
The emergence of phreaking, a form of telecommunication manipulation, has had a significant impact on society. Phreakers, also known as phone hackers or phone phreaks, have exploited vulnerabilities in the telephone system to manipulate calls and signals for various purposes.
One of the most noticeable impacts of phreaking is in the realm of security. Phreakers have demonstrated the fragility of telecommunication networks, exposing weaknesses that could be exploited by hackers for malicious purposes. This has forced telecommunication companies to invest heavily in improving the security of their infrastructure and implementing measures to prevent unauthorized access.
Phreaking has also affected the way people communicate. The ability to manipulate phone signals has allowed phreakers to perform pranks, such as making free long-distance calls or impersonating others. This has disrupted normal communication channels and caused inconvenience to individuals and businesses.
Furthermore, phreaking has influenced the development of digital technology. The early exploits and innovations of phreakers paved the way for advancements in telephony and communication systems. Their understanding of the underlying technology and their ability to manipulate it contributed to the development of more secure and efficient networks.
However, the negative impact of phreaking cannot be overlooked. The act of wiretapping and eavesdropping on private phone conversations has raised serious concerns about privacy and data protection. The vulnerabilities that phreakers exploit highlight the need for stronger security measures to protect personal and sensitive information.
In conclusion, phreaking has had a multifaceted impact on society. It has brought attention to the vulnerabilities in telecommunication networks, influenced the development of technology, and disrupted normal communication channels. However, it has also raised serious security and privacy concerns that need to be addressed.
Influence on Telecommunications Industry
The world of phreaking has had a significant influence on the telecommunications industry. Phreaking, which is a term derived from the combination of “phone” and “freak,” refers to the exploration and exploitation of vulnerabilities in telecommunication networks.
Phreakers, who are hackers specialized in telephony, have played a crucial role in highlighting the security weaknesses of telecommunication systems. By uncovering vulnerabilities, phreakers have contributed to the improvement of telecommunication technology and the implementation of stronger security measures.
One of the main impacts of phreaking on the telecommunications industry is the increased focus on network security. Phreakers have demonstrated how vulnerabilities in telecommunication networks can be exploited for cybercrime purposes, such as fraud, wiretapping, and digital signal manipulation. These activities have led telecommunication companies to invest resources in developing more secure telephony systems and protocols.
Moreover, phreaking has also influenced the evolution of telecommunication fraud detection and prevention techniques. Phreakers have used their expertise to identify and exploit weaknesses in billing systems, leading to significant financial losses for telecommunication providers. As a result, telecommunication companies have improved their fraud detection and prevention mechanisms to minimize such incidents.
Additionally, phreaking has had a more subtle impact on the telecommunications industry through its influence on prank calls. Phreakers were known for making elaborate and technically advanced prank calls, showcasing their skills and challenging the limits of telephony. This has led to the development of technologies and features to trace and prevent malicious or prank calls, enhancing the overall security and reliability of telecommunication systems.
In conclusion, phreaking has left a lasting impact on the telecommunications industry. Through their exploration and exploitation of vulnerabilities, phreakers have pushed for advancements in telecommunication technology, network security, fraud detection, and call tracing. Their activities have played a significant role in shaping the current landscape of telephony and ensuring the security of digital communication.
Legacy of Phreaking in the Digital Age
Phreaking, the manipulation of telecommunication systems to exploit vulnerabilities in the network, has left a lasting impact on the digital age. While phreaking emerged in the era of analog telephony, its techniques and concepts continue to shape the world of cybersecurity and communication in the digital era.
The legacy of phreaking can be seen in the heightened focus on security in digital communication. Phreakers were pioneers in exposing weaknesses in telephone networks, which led to the development of stronger security measures to protect against wiretaps and signal fraud. Today, this legacy is evident in the rigorous security protocols employed by organizations to safeguard their digital networks and sensitive information.
Phreaking also paved the way for the development of modern cybercrime. The techniques used by phreakers, such as phone manipulation and exploiting vulnerabilities in telecommunication systems, laid the foundation for the hacker community. Phreakers were among the first to understand the potential of technology to be used for illegal activities, thus influencing the future direction of cybercriminal endeavors.
Despite its roots in illegal activity, phreaking fostered a sense of curiosity and experimentation that continues to drive technological innovation. Many phreakers transitioned into legitimate careers in technology and played key roles in the development of digital networks and communication infrastructure. The knowledge and skills gained through phreaking have proven invaluable in uncovering and addressing vulnerabilities in the ever-evolving digital landscape.
Overall, the legacy of phreaking in the digital age extends beyond its initial pranks and exploits. It has shaped the way we think about security, communication, and technology, and has had a profound influence on the development of the hacker community and the fight against cybercrime. Phreaking serves as a reminder of the importance of staying vigilant and proactive in protecting our digital networks and information in an increasingly interconnected world.
FAQ about topic “Understanding the World of Phreaking: Exploring the Origins and Techniques of Phreakers”
What is phreaking?
Phreaking is the practice of exploring and manipulating the telecommunications system to make free phone calls, bypass billing systems, or gain unauthorized access to information. It originated in the 1970s and has evolved alongside advancements in technology.
How did phreaking begin?
Phreaking began in the 1970s when a group of hackers, known as phreakers, discovered that certain whistling tones could manipulate the telephone system and make free long-distance calls. These initial discoveries sparked the curiosity of others and the phreaking community grew from there.
What techniques do phreakers use?
Phreakers use various techniques to manipulate the telecommunications system. These include tone dialing, blue boxes, red boxes, and even social engineering tactics. Tone dialing involves producing specific tones to access certain system features, while blue boxes and red boxes are electronic devices used to bypass billing systems and make free calls. Social engineering involves manipulating individuals to gain access to confidential information, such as passwords or account details.
Is phreaking illegal?
Yes, phreaking is illegal in most countries as it involves unauthorized access to and manipulation of telecommunication systems. Phreaking activities can lead to criminal charges, including hacking, fraud, and theft of services.
Has phreaking evolved with advancements in technology?
Yes, phreaking has evolved alongside advancements in technology. As telecommunication systems have become more sophisticated, phreakers have adapted their techniques to exploit vulnerabilities in the system. Nowadays, phreaking activities also extend to digital networks and mobile devices, with phreakers finding new ways to bypass security measures and gain unauthorized access to information.

